Estimated reading time: 8 minutes
Key Takeaways
- Elliptic Curve Cryptography (ECC) provides robust security with smaller keys.
- It leverages the elliptic curve discrete logarithm problem for data protection.
- Significantly more efficient than many traditional algorithms like RSA.
- Widely adopted for digital signatures, secure key exchanges, and encryption.
- Increasingly essential for mobile, IoT, and cryptocurrency security.
Table of Contents
Understanding Elliptic Curve Theory
Elliptic Curve Cryptography (ECC) has become a leader in modern public key cryptography,
transforming secure data transmission across various digital platforms. This advanced
cryptographic method leverages the intricate mathematical properties of elliptic curves
to provide robust security with smaller key sizes compared to traditional algorithms
like RSA. As our digital landscape continues to evolve, ECC’s efficiency and strength
make it an increasingly essential tool for safeguarding sensitive information.
In this comprehensive guide, we explore the world of Elliptic Curve Cryptography,
examining its fundamental principles, applications, and the reasons behind its
growing popularity in the realm of cybersecurity.
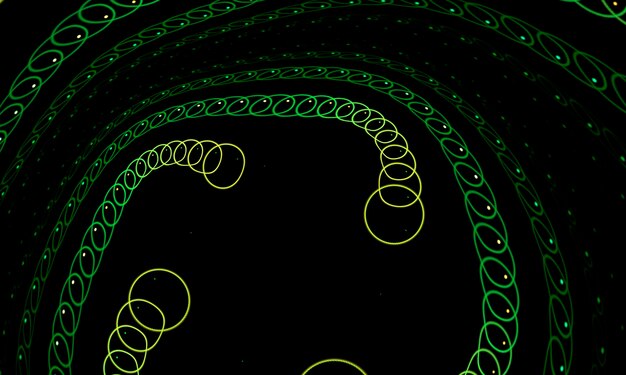
At the heart of ECC lies the fascinating world of elliptic curves and finite fields.
These mathematical concepts form the backbone of this cryptographic method, providing
the robust security that makes ECC so effective.
Elliptic Curves:
• An elliptic curve is defined by the equation y² = x³ + ax + b, where
a and b are constants.
• These curves possess unique symmetry and mathematical properties ideal for
cryptographic applications.
• The shape and characteristics of elliptic curves allow for complex computations
that are difficult to reverse, forming the basis of ECC’s security.
Finite Fields:
• Finite fields provide the algebraic structure essential for ECC operations.
• These mathematical constructs limit the range of numbers used in calculations,
enhancing the security of the cryptographic system.
• The use of finite fields in ECC enables high levels of security while maintaining
computational efficiency.
The robustness of elliptic curve theory in cryptographic applications stems from
combining these mathematical elements, creating a system that’s both secure and efficient.
ECC Algorithm
The ECC algorithm distinguishes itself among cryptography methods with its unique
approach to ensuring data security. Unlike traditional algorithms, ECC relies on
the elliptic curve discrete logarithm problem (ECDLP) to safeguard information.
Algorithm Overview:
• ECC utilises the difficulty of solving the ECDLP to create secure cryptographic systems.
• Compared to RSA, ECC requires significantly smaller key sizes to achieve equivalent
levels of security.
• This size difference translates to faster computations and more efficient use of
computational resources.
Efficiency and Security Benefits:
• ECC provides quicker encryption and decryption processes due to its streamlined calculations.
• The algorithm’s efficiency makes it ideal for environments with limited computational power,
such as mobile systems and IoT solutions.
• Despite using smaller keys, ECC maintains a high level of security, often surpassing that
of traditional methods.
Research has consistently shown that ECC outperforms many traditional cryptographic methods in
both efficiency and security, making it an increasingly popular choice for modern cybersecurity
solutions (see research).
Encryption Techniques with ECC
Elliptic Curve Cryptography offers a range of powerful encryption techniques that
ensure secure data transmission across various platforms and applications.
Encryption Methods:
• The Elliptic Curve Integrated Encryption Scheme (ECIES) is a popular
ECC-based encryption method.
• ECC is often combined with symmetric encryption algorithms to enhance overall
data protection.
• This hybrid approach leverages the strengths of both ECC and symmetric encryption,
providing robust security with efficient performance.
Secure Data Transmission:
• ECC ensures high levels of security for data in transit, using minimal computational resources.
• Applications of ECC in secure data transmission include:
– Secure web communications (HTTPS)
– Email encryption
– Secure data storage solutions
Real-world implementations have demonstrated the effectiveness of ECC-based encryption
in providing strong protection for sensitive information across various digital platforms.
Digital Signatures in ECC
Digital signatures play a crucial role in maintaining data integrity and authenticity
in the digital world. ECC offers powerful digital signature capabilities through
the Elliptic Curve Digital Signature Algorithm (ECDSA).
Creating and Verifying Signatures:
1. The process begins by hashing the message to be signed.
2. The hash is then encrypted using the sender’s private key.
3. The recipient can verify the signature using the sender’s public key.
Significance of Digital Signatures:
• ECC-based digital signatures ensure that messages have not been tampered with during transmission.
• They provide proof of the sender’s identity, crucial for secure transactions and communications.
• In cryptocurrencies like Bitcoin and Ethereum, ECC digital signatures are fundamental to
maintaining the integrity and security of transactions.
Research has shown that ECC-based digital signatures offer a high level of security
and reliability, making them a preferred choice for many modern cryptographic applications.
Key Exchange Protocols
Secure key exchange is vital for establishing encrypted communications between parties.
ECC provides efficient and secure key exchange protocols that outperform many
traditional methods.
ECC-Based Key Exchange:
• The Elliptic Curve Diffie-Hellman (ECDH) protocol is a widely used ECC-based key
exchange mechanism.
• ECDH allows two parties to securely agree on a shared secret key over an insecure channel.
• This shared key can then be used for symmetric encryption of further communications.
Comparison with Other Methods:
• ECC-based key exchange protocols offer several advantages over traditional methods
like RSA:
– Smaller key sizes for equivalent security levels
– Reduced computational overhead
– Faster key generation and exchange processes
The superior performance and security of ECC in key exchange scenarios have been
well-documented in numerous studies, highlighting its effectiveness in modern
cryptographic systems.
Cryptographic Keys Management
Proper management of cryptographic keys is essential for maintaining the security
of any cryptographic system, including those based on ECC.
Key Generation and Distribution:
• ECC key generation involves complex mathematical processes to ensure randomness
and uniqueness.
• Secure distribution of ECC keys often utilises key exchange protocols like ECDH.
• The smaller key sizes in ECC make key distribution more efficient compared
to traditional methods.
Best Practices:
• Secure key storage: Implement robust solutions to protect private keys from
unauthorised access.
• Regular key updates: Periodically rotate keys to mitigate the risk of key compromise.
• Secure key exchange: Use proven protocols like ECDH for safe key distribution.
• Access control: Implement strict measures to control access to cryptographic keys.
Research findings emphasise the importance of following these best practices
to maintain the integrity and security of ECC-based cryptographic systems.
Applications of Elliptic Curve Cryptography
ECC has found widespread adoption across various industries, thanks to its efficiency
and robust security features.
Real-World Applications:
Banking and Finance:
• Securing online transactions
• Protecting sensitive financial data
• Enhancing the security of mobile banking applications
Web Security:
• Enabling HTTPS connections in web browsers
• Securing API communications
• Protecting user data in cloud services
Cryptocurrencies:
• Facilitating secure transactions in Bitcoin, Ethereum, and other digital currencies
• Verifying ownership and authenticity of digital assets
Internet of Things (IoT):
• Providing lightweight encryption for resource-constrained systems
• Securing communications between IoT systems and central servers
Secure Communications and Transactions:
• In cryptocurrencies, ECC ensures the security and authenticity of each transaction
through digital signatures.
• For secure web communications, ECC is integral to the TLS (Transport Layer Security)
protocol, establishing encrypted connections between clients and servers.
The widespread adoption of ECC across these diverse applications underscores its
effectiveness in enhancing security in various technological domains.
Advantages of ECC
Elliptic Curve Cryptography offers several key advantages that have contributed to its
growing popularity in the field of public key cryptography.
Key Benefits:
• Smaller key sizes: ECC requires significantly smaller keys compared to
traditional algorithms like RSA for equivalent security levels.
• Reduced storage and bandwidth requirements: Smaller keys mean less data
to store and transmit.
• Faster computations: ECC enables quicker encryption and decryption processes,
enhancing overall system performance.
• Equivalent or superior security: Despite smaller key sizes, ECC provides
robust security comparable to or better than traditional methods.
Role in Advancing Public Key Cryptography:
• ECC contributes to the evolution of public key cryptography by offering more efficient
and scalable security solutions.
• Its resilience against growing computational power makes it a future-proof option for
long-term security needs.
• ECC’s efficiency in resource-constrained environments makes it ideal for emerging
technologies like IoT and mobile computing.
Research consistently highlights the superiority of ECC in terms of efficiency and security,
cementing its importance in modern cryptographic practices.
Conclusion
Elliptic Curve Cryptography has established itself as a cornerstone of modern secure
data transmission and public key cryptography. Its unique combination of robust security,
computational efficiency, and versatility makes it an invaluable tool in our increasingly
interconnected digital world.
From securing online banking transactions to enabling secure communications in various
industries, ECC plays a vital role in today’s digital security landscape.
FAQs
What makes ECC more efficient than RSA?
ECC uses smaller key sizes to achieve comparable security, resulting in faster
computations and reduced bandwidth requirements.
How do elliptic curves enhance cryptographic security?
Elliptic curves introduce complex mathematical challenges that make reversing ECC
computations highly impractical, ensuring stronger data protection.
Why is ECC popular in cryptocurrency applications?
ECC-based digital signatures provide secure transaction verification with minimal
computational overhead, making them ideal for blockchain networks.
Is ECC suitable for resource-constrained devices?
Yes, ECC’s smaller key sizes and efficient computations make it well-suited for
IoT and mobile devices with limited processing capabilities.
How does ECC compare to other modern cryptographic methods?
ECC often outperforms many alternatives in speed and security, particularly when
dealing with limited resources or high transaction volumes.
Can ECC be combined with other encryption algorithms?
Absolutely. ECC is frequently used alongside symmetric encryption methods,
forming a hybrid approach to maximize both security and performance.
How do I ensure secure key management in ECC?
Implement best practices like ECDH for key exchange, store private keys
securely, and regularly rotate keys to maintain robust security.
Are there any drawbacks to using ECC?
While ECC is highly efficient, it does require careful implementation to
avoid potential vulnerabilities. Properly audited libraries and consistent
best practices can mitigate risks.
Where can I learn more about ECC standards and protocols?
The NIST FIPS 186-4
outlines ECC standards, and additional resources are available through
industry publications and academic research.
Is ECC future-proof?
ECC is considered more resistant to quantum attacks than some older methods,
though research is ongoing. Its smaller key sizes and adaptability
position it strongly for future cryptographic needs.









